Tag Archive for: Passwords
Password Managers vs Native Browser Apps
Business, Tech TipsFeeling overwhelmed managing all your passwords? Dive into our latest blog post where we compare professional password managers with native browser storage!

How Do Passwordless Logins Work?
Business, Tech TipsPasswordless authentication is frequently used to strengthen security and lower the cost and complexity of IT operations.

5 Best Practices for Implementing an Effective MFA Strategy
News
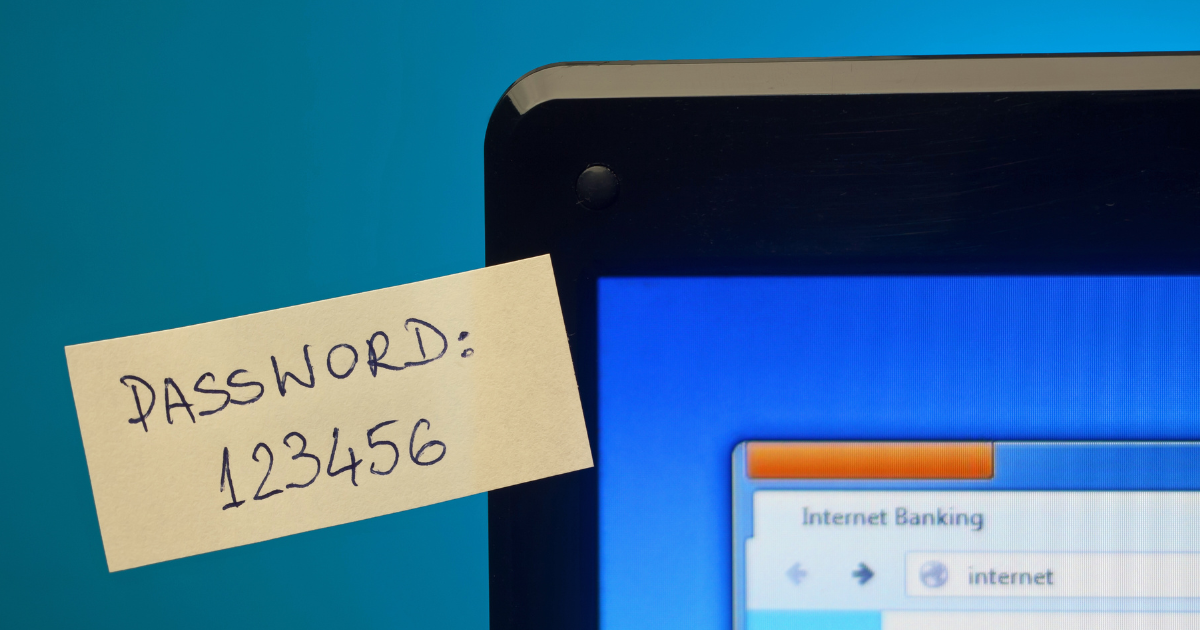
Bad password habits are extremely common. Unfortunately, they are often the cause of data breaches or cloud account takeovers. People have so many passwords to juggle that they often use weak passwords, store passwords using non-secure…

Best Practices for Disabling, Deleting & Locking Down Past Employee Accounts
Business If you leave a former employee’s accounts active, you’re leaving your network and data at risk. You should immediately delete, disable, or shut down former employee accounts.
