Tag Archive for: multifactor authentication
Password Managers vs Native Browser Apps
Business, Tech TipsFeeling overwhelmed managing all your passwords? Dive into our latest blog post where we compare professional password managers with native browser storage!

5 Ways to Protect Your Company’s SaaS Data
Business, IT Partner, Tech TipsDive into the world of SaaS security, understand the nuances of its rapid evolution, and arm yourself with the best strategies to safeguard your business’s data.

Is Your Team Aware of These New ChatGPT Phishing Scams?
Business, Tech TipsExplore how criminals are leveraging ChatGPT to perpetrate phishing scams and provide valuable tips for spotting and avoiding these attacks.

Top 5 Cybersecurity Risks for Remote Teams & How to Address Them
Business, IT Partner, Tech TipsDiscover how the shift to remote teams introduces unique challenges in cybersecurity and protecting sensitive data.

How to Improve Cloud Security with Phishing-Resistance MFA
Business, IT Partner, Tech TipsAdopting preventive security precautions, like the phishing-resistance MFA is imperative given cyberattacks' growing magnitude and expense.

How to Not Sacrifice User Convenience When Setting Up Authentication Security
Business, IT Partner, Tech TipsAdopting MFA (Multi-factor authentication) is now the trending standard for access security and authentication.

How Do Passwordless Logins Work?
Business, Tech TipsPasswordless authentication is frequently used to strengthen security and lower the cost and complexity of IT operations.

4 Helpful Technology Resolutions to Make for the New Year
Business, Tech Tips
With a new year comes new opportunities, new challenges, and new goals. Many of us make new year's resolutions from a personal perspective. Maybe we plan to go to the gym more, eat healthier or even use our cars less. While these are all…

6 Questions You’ll Need to Answer If Applying for Cybersecurity Insurance
Business, IT Partner
The cybersecurity landscape seems to get more dangerous every year. Besides having to deal with a COVID-pandemic over the last 18+ months, there has also been a cyber pandemic. That pandemic has included an increase in cloud account attacks…

5 Best Practices for Implementing an Effective MFA Strategy
News
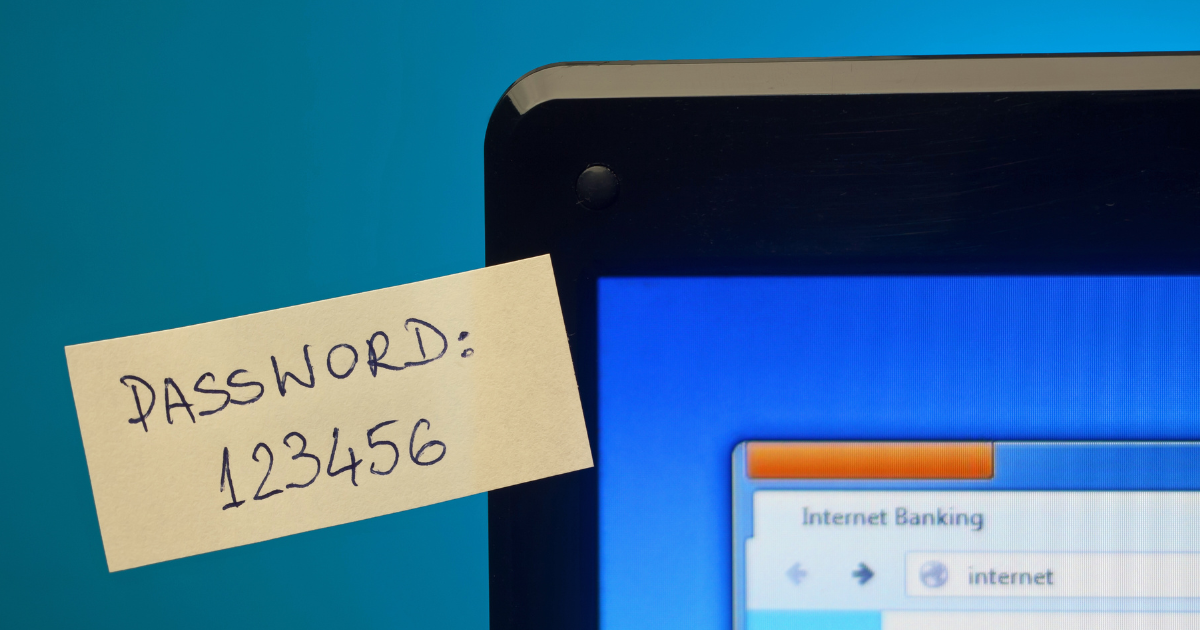
Bad password habits are extremely common. Unfortunately, they are often the cause of data breaches or cloud account takeovers. People have so many passwords to juggle that they often use weak passwords, store passwords using non-secure…
